Cracking the Code — Algorithms to Quantum Keys
🔄Recap of Algorithms for Symmetric and Asymmetric Cryptography
Asymmetric Algorithms
🎯 Concept Focus - What we’ll nail today
Detailed understanding of Symmetric Algorithms
DES, Feistel intuition, key sizes and why DES retired
Block modes (ECB, CBC, CFB, OFB, CTR), IVs, and error propagation
2DES and the Meet-in-the-Middle problem
AES vs RC4 (where stream vs block matters)
Detailed Understanding of Asymmetric Algorithms
Asymmetric basics: what the two keys actually do
RSA (math posture, practical attacks, key sizes)
Diffie–Hellman & ElGamal (key agreement vs encryption)
ECC (security-per-bit and why IoT loves it)
Hybrid Crypto
Quantum Key Distribution (physics as a security primitive)
Key management, dual control, split knowledge, separation of duties
Detailed understanding of Symmetric Algorithms
DES — why it mattered and why it’s gone
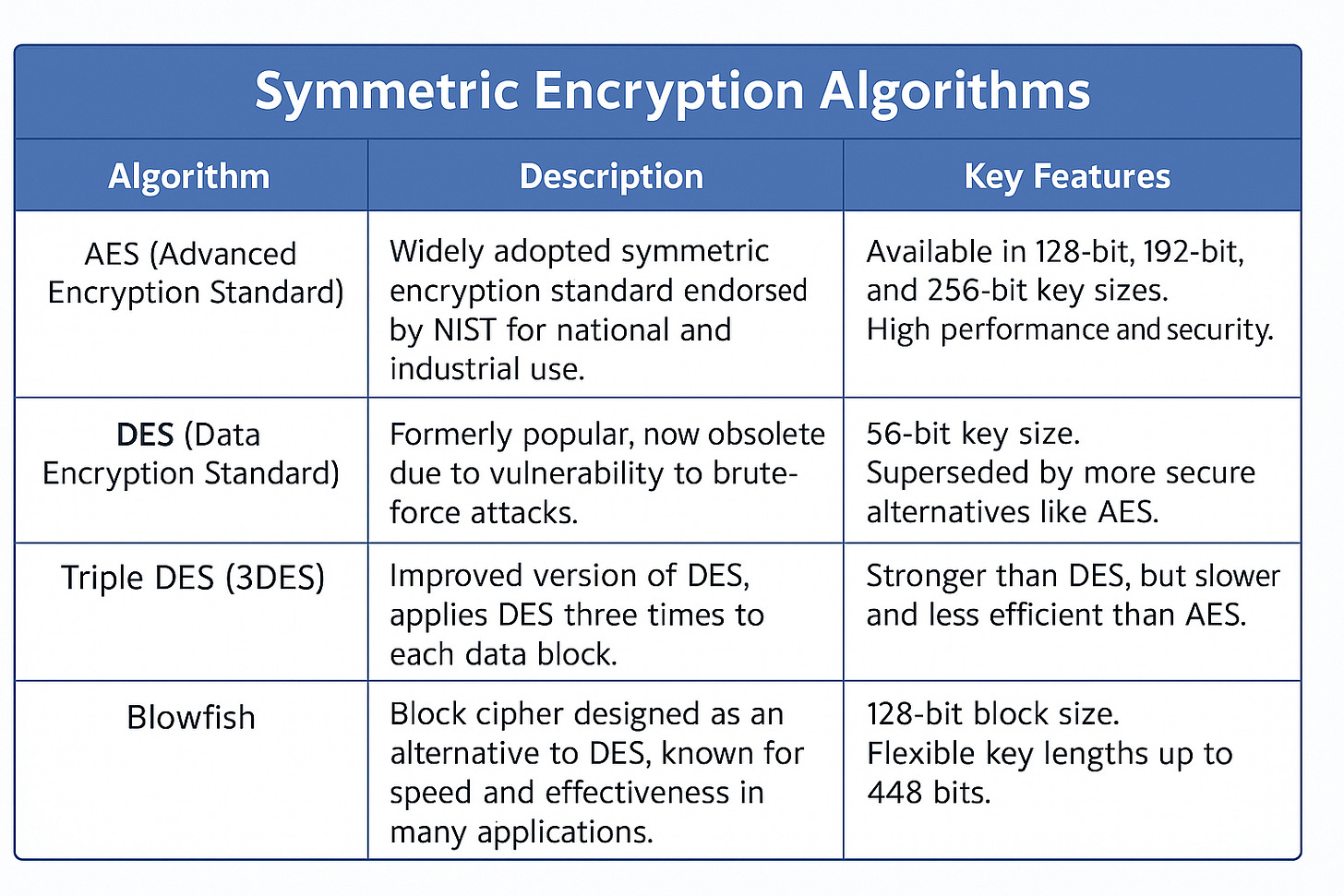
DES is one of the earliest symmetric encryption algorithms, developed in the 1970s.
The algorithm divides the input plaintext block into two halves.
One half of the block is used to modify the other half through a series of rounds.
Each round applies operations like Exclusive-OR (XOR), substitutions, and permutations to alter the data.
DES uses a 56-bit key and operates on 64-bit blocks.
Strengths: It was a strong standard for its time and widely adopted.
Weaknesses: Advances in computing made its 56-bit key length vulnerable to brute-force attacks, leading to its eventual replacement by stronger algorithms like AES.
ECB Electronic Code Block used as Very short messages 64 bit such as transmission of a DES key
no IV; identical blocks → identical ciphertext. Use only for tiny, non-repeating data or test vectors.
CBC Cipher Block Chaining used as Authentication
needs unpredictable IV; error propagates one block forward; adds authenticity signal characteristics.
CFB Cipher Feedback used as Authentication
stream-like; uses IV; error propagates.
OFB Output Feedback used as Authentication
stream-like; uses IV; no error propagation.
CTR Counter used in high speed applications like IPSec
nonce + counter; parallelizable; great for audio/video/high-throughput.
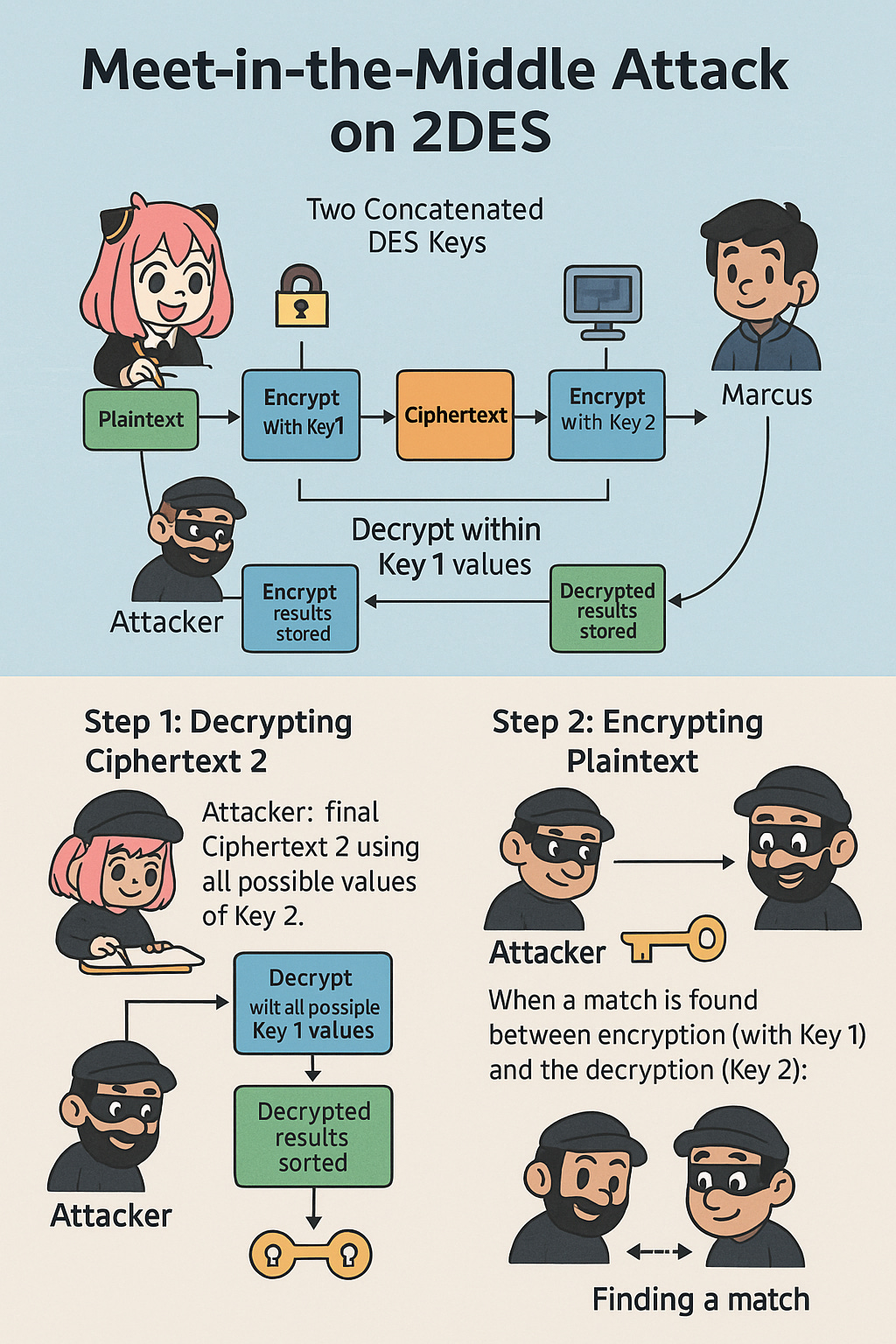
2DES was designed to enhance the security of DES by applying it twice with two different keys
Double DES Encryption Process:
Two concatenated DES keys (Key 1 and Key 2) are used for encryption.
Plaintext is first encrypted using Key 1, producing an intermediate result called Ciphertext "m".
Ciphertext "m" is then encrypted again using Key 2 to produce the final Ciphertext 2, which is sent to the receiver.
Meet-in-the-Middle Attack Concept
The MitM attack is a cryptanalytic technique that targets block ciphers like 2DES to reduce the effective security provided by the two encryption layers. The attack leverages the fact that intermediate results (like Ciphertext "m") can be matched from both ends of the encryption/decryption process.
Attack Steps (Operation within 2DES Cryptosystem):
AES & RC4
AES was developed by the NIST in 2001 to replace the DES, which became vulnerable to attacks due to its short key length (56 bits) and computational advances. AES divides the message into blocks of 128 bits (or 16 bytes). It uses a chosen key (e.g., 256 bits) and applies 14 rounds of encryption (substitution, permutation, and mixing) to transform the plaintext into ciphertext.
Low processing overhead, making it efficient.
Versatile, meaning it works well in different hardware and software environments.
AES supports three different key sizes: 128 bits ,192 bits , 256 bits
All variations work with a fixed block size of 128 bits.
128-bit key: 10 rounds of encryption
192-bit key: 12 rounds of encryption
256-bit key: 14 rounds of encryption
Strengths :
It is highly secure due to its key lengths, making brute-force attacks infeasible.
It’s efficient and fast in both hardware and software implementations.
It has become the standard for encrypting sensitive data, used in applications like VPNs, SSL/TLS, disk encryption, and wireless security (e.g., WPA2).
AES is more secure than RC4 because of key size difference
RC4 Encryption:
RC4 (Rivest Cipher 4) is a stream cipher that uses a variable-length key for encrypting data.
It is fast and simple, making it suitable for various applications.
If RC4 is used with a key length of at least 128 bits, there are currently no practical attacks against the algorithm itself. ○
The attacks on RC4 in WEP (Wired Equivalent Privacy) applications are not due to inherent weaknesses in RC4 but rather poor implementation practices:
WEP reuses keys, leading to vulnerabilities.
Initialization vectors (IVs) in WEP are short and often predictable, making attacks feasible.
Detailed understanding of Asymmetric Algorithms
Characteristics of Asymmetric Algorithms:
● One-way Functions:
○Asymmetric algorithms rely on mathematical functions that are easy to compute in one direction (forward) but computationally infeasible to reverse (backward or reverse-engineer).
Example: Multiplying two large prime numbers is straightforward, but factoring the product back into the primes is extremely difficult (basis for RSA).
● Ease of Public Key Generation:
The process to generate a public key from a private key (forward process) is relatively simple.
However, determining the private key from the public key (reverse process) is computationally hard.
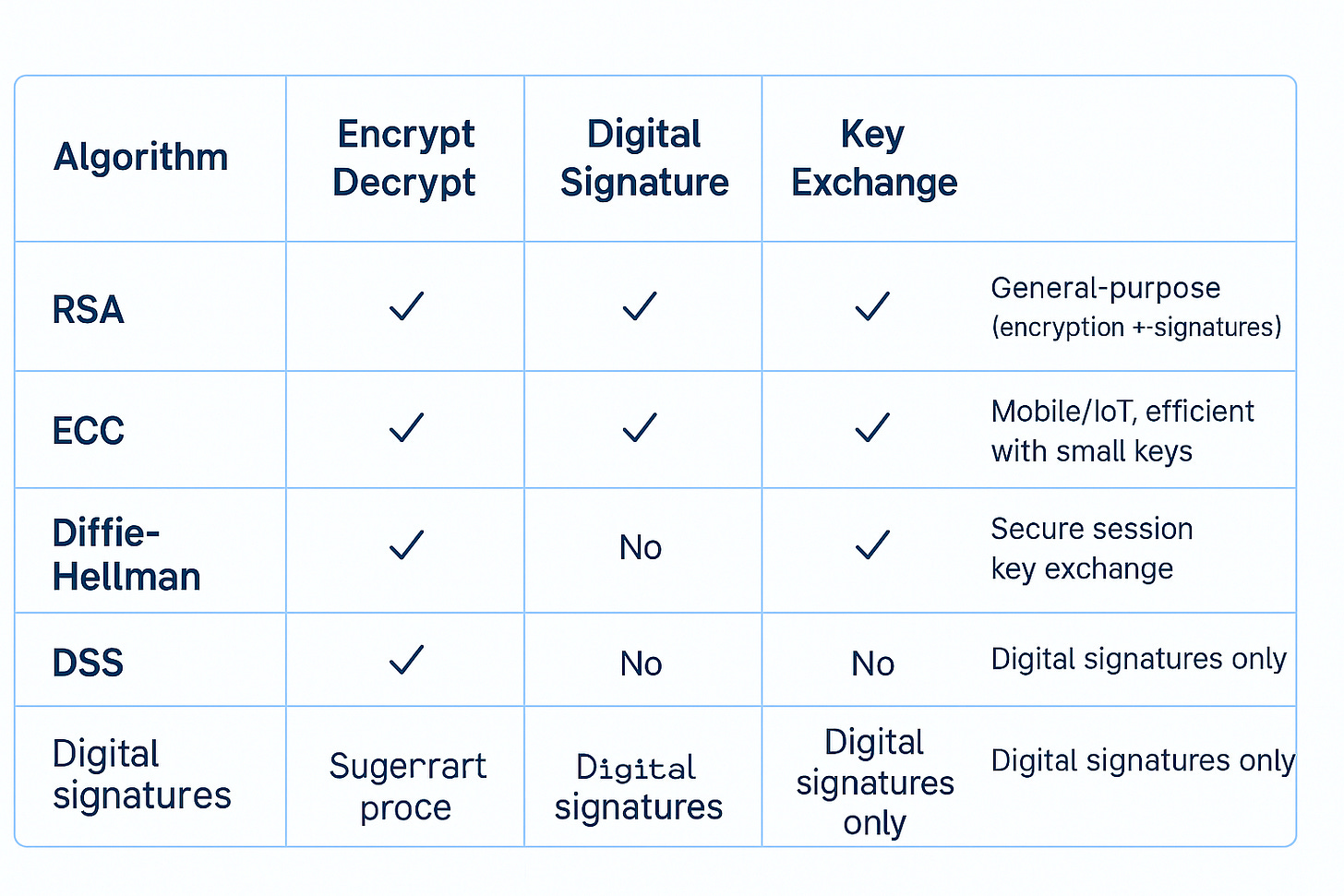
RSA
Oldest and most secure asymmetric algorithm (still widely used).
Created in 1978 at MIT by Rivest, Shamir, and Adleman.
Mathematical foundation:
Easy to multiply two large primes.
Extremely hard to factor the product back into those primes.
Security depends on:
Difficulty of factoring large integers.
Key size selection (≥2048 bits today).
Competes with other asymmetric algorithms:
RSA vs ECC → RSA needs much larger keys for same strength; ECC is more efficient.
DH vs ElGamal → DH for key exchange, ElGamal extends DH but with larger ciphertexts.
Use Cases
Encryption → ensures confidentiality.
Digital Signatures → ensures authenticity + integrity.
Key Exchange → securely transports session keys.
Advantages of RSA
Supports both encryption and digital signatures (versatile).
Widely deployed: SSL/TLS, PGP, S/MIME, VPNs.
Proven, mature, and standardized.
Primary Attack Approaches
Brute-force attacks
Try all possible private keys.
Impractical with 2048-bit or higher keys.
Mathematical attacks
Factorization of large prime products.
Threat from future advances in quantum computing.
Timing / Side-channel attacks
Exploit variations in computation time to infer key information.
Mitigated by constant-time algorithms and hardened implementations.
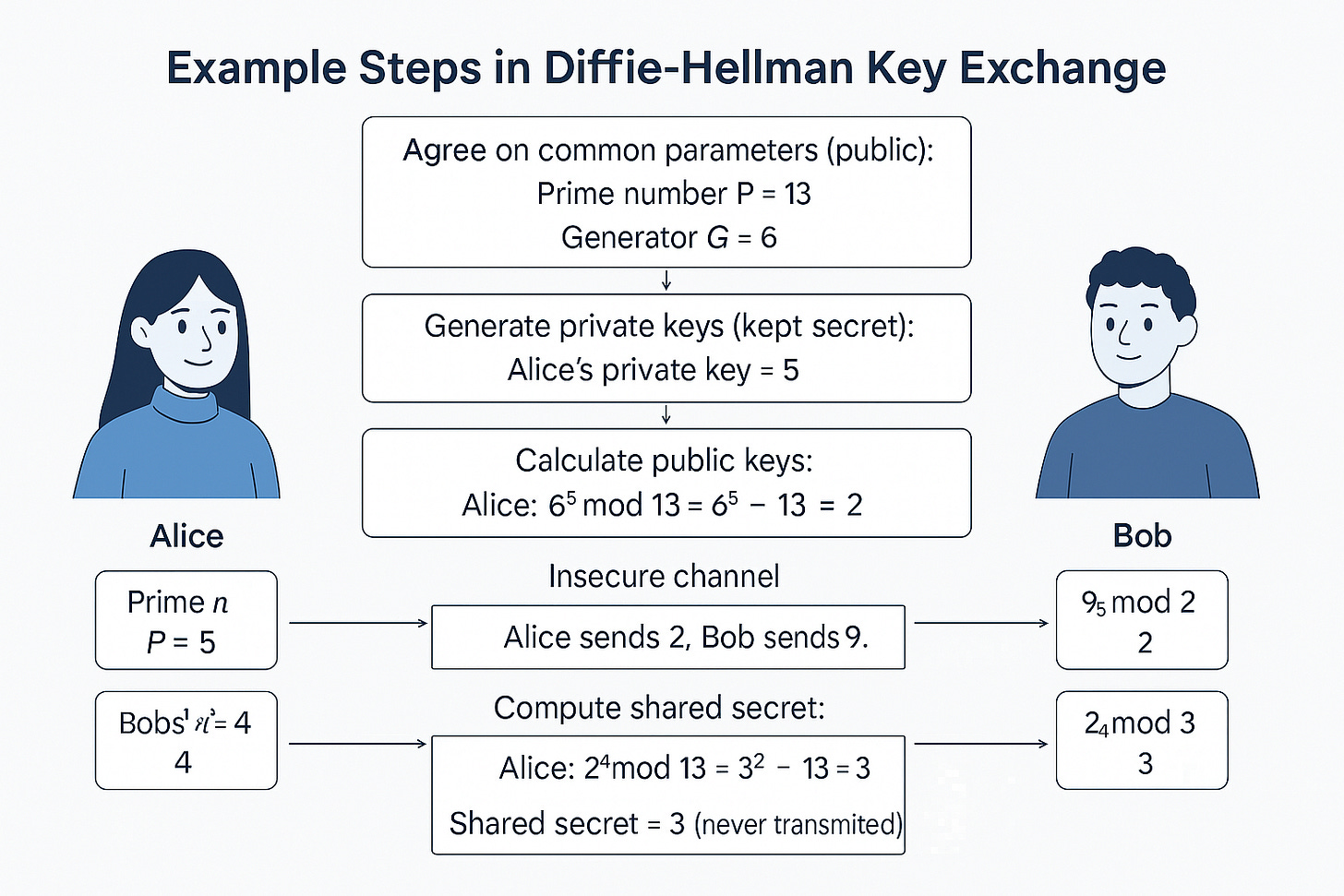
Diffie Hellman Algorithm & EL Gamal
Establishes a shared symmetric key between two parties over an insecure channel.
Used for later symmetric encryption (DH itself does not encrypt messages).
Common in PKI, TLS/SSL handshakes, IPSec (VPNs).
Core Concept
Security rests on the Discrete Logarithm Problem (DLP):
Given a public key, base (G), and prime modulus (P), it is computationally infeasible to derive the private key.
Provides confidentiality of the shared secret without directly transmitting it.
Example Steps in DH Key Exchange
Applications
TLS/SSL → secure web communication.
IPSec → VPN tunnels.
Secure key agreement in many distributed systems.
Advantages
Securely derives a shared secret even over insecure channels.
Resistant to eavesdropping (without authentication bypass).
Efficient for session key generation.
Limitations
No Authentication → vulnerable to MitM attacks.
Mitigation: combine with RSA/ECC signatures or digital certificates.
No direct encryption → DH only negotiates keys, not confidentiality itself.
High computational cost with very large numbers (less of an issue with ECC-based DH).
Elliptic Curve Cryptography (ECC)
Same security as RSA, with much smaller keys.
Requires less compute power and less bandwidth, making it ideal for:
Mobile devices
IoT / Industrial Control Systems (ICS)
Constrained environments
Key Points
Highest strength per bit
Example: 256-bit ECC ≈ 3072-bit RSA.
Smaller keys → faster, lighter, equally secure.
Versatile use cases
Confidentiality → data encryption.
Digital Signatures → authenticity + integrity.
Message Authentication → detect tampering.
Efficiency benefits
Shorter keys save CPU, battery, and network bandwidth.
Perfect for TLS on mobile, certificates, and IoT crypto.
Hybrid Cryptography
A combination of two worlds:
Symmetric encryption → fast, efficient for large data.
Asymmetric encryption → secure for key exchange.
Together, they deliver speed + security.
Process (Step by Step)
Encrypt the Message (Symmetric)
Sender chooses a symmetric key (SK).
Message is encrypted with SK → Encrypted Message.
Symmetric encryption chosen for efficiency.
Encrypt the Symmetric Key (Asymmetric)
Sender encrypts the SK with receiver’s public key.
Produces Encrypted SK.
Asymmetric ensures SK is shared securely.
Transmit Both
Sender sends: [Encrypted Message + Encrypted SK] over the channel.
Receiver’s Side
Receiver uses private key to decrypt Encrypted SK → gets SK.
Receiver then uses SK to decrypt Encrypted Message → retrieves original plaintext.
Why It Works
Efficiency → symmetric for bulk data.
Security → asymmetric ensures safe key transport.
Best of both worlds → secure + scalable.
Real-World Applications
SSL/TLS (HTTPS) → handshake uses asymmetric; session data uses symmetric.
Encrypted Emails (PGP, S/MIME) → message + wrapped key.
Digital Wallets / Online Banking → secure key transmission for transactions.
Quantum Cryptography
1. Definition
A set of protocols and systems that use quantum mechanics to securely create and distribute secret keys.
Different from traditional cryptography:
Traditional → based on mathematical hardness (factoring, discrete logs).
Quantum crypto → based on laws of physics.
2. Physics-Based Security
Uses properties of photons (polarization, spin) instead of math.
Security rests on physical principles:
Heisenberg Uncertainty Principle → measuring a quantum state disturbs it.
No-Cloning Theorem → quantum information cannot be copied exactly.
If an attacker tries to intercept, the state collapses, alerting sender/receiver.
3. Quantum Key Distribution (QKD) Process
Roles: Alice (sender), Bob (receiver), Eve (eavesdropper).
Key Generation
Alice generates an encryption key via a quantum state generator.
Encoded in photons (polarization/spin).
Transmission
Key sent over a Quantum Channel (fiber optics / free space).
Any eavesdropping (by Eve) disturbs photons → detectable.
Reception
Bob receives with a quantum state detector.
If no interference, he gets the same key.
Public Channel
Actual encrypted message (ciphertext) is transmitted over normal internet/phone lines.
Security comes from the quantum-protected key, not the channel.
4. Security Benefits of QKD
Unconditional security → eavesdropping can’t go undetected.
Resistant to quantum computers → unlike RSA/ECC, no reliance on factorization or discrete logs.
Eavesdropper detection → if Eve tampers, Alice & Bob discard the key and retry.
5. Limitations
Still research/experimental; not mainstream yet.
Used only for key exchange, not for encrypting bulk data.
Infrastructure-heavy (requires quantum channels, detectors).
Key Management
A cryptosystem must remain secure even if everything about it is public, except the key.
Security depends only on the secrecy of the key, not the secrecy of the algorithm.
Challenges
Secure generation → keys must be random, strong.
Distribution → share keys only with intended recipients.
Storage → protect in HSMs or secure KMS.
Rotation → update keys periodically.
Revocation → replace expired/compromised keys immediately.
Manual vs Automatic
Manual → human handling, error-prone.
Automatic → automated key lifecycle management → scalable + consistent.
Operational Controls
Dual Control → two people act together (e.g., two officers turning keys simultaneously).
Split Knowledge → no single person holds full key; fragments must be combined.
Separation of Duties → no single person controls all tasks in a sensitive process.
Key Escrow → keys held in trust for recovery or compliance.
How They Work Together
Split Knowledge → no one knows the whole key.
Dual Control → multiple people needed to reassemble/use it.
Together, reduce insider threat and enforce least privilege.
🧠 Brain Ticklers
Q1. A build system signs artifacts. Anya wants authenticity and non-repudiation without leaking code. Which change best aligns?
A) Encrypt artifacts with the CI server’s public key
B) Hash artifacts with SHA-256 and publish the digest
C) Sign the digest with the CI’s private key and publish signature + artifact
D) Encrypt artifacts with developers’ private keys
Q2. A legacy service uses CBC with a static IV. What’s the most accurate risk characterization?
A) Only performance impact
B) Identical plaintext blocks are linkable across sessions
C) Padding oracle is guaranteed
D) Error propagation disappears
-Q3. Neuromesh trials 2DES for “112-bit security.” Marcus objects. Why?
A) 2DES is slower than AES only
B) Meet-in-the-Middle reduces effective work to about 2⁵⁷
C) 2DES requires three keys, not two
D) 2DES can’t run in CBC
Q4. Anas proposes raw Diffie–Hellman for a device onboarding channel. What is the primary missing property?
A) Confidentiality
B) Integrity
C) Authentication of peers
D) Forward secrecy
Q5. For HSM key recovery, which pairing is best practice?
A) Key escrow only
B) Dual control only
C) Split knowledge only
D) Split knowledge + dual control
Follow the Series - https://parulsharma491089.substack.com/p/cryptography-decipher-the-art-of
#CISSP #CyberSecurity #InfoSec #SecurityLeadership #WomenInCyberforce #WomenInTech #AnyaInCyberSecurity #FromDevToDefender #TechLeadership #DevSecOps #CISSPDomains #Cryptography #AES #RSA #ECC #TLS #KeyManagement #Governance