📡 Protocols That Actually Keep You Safe
🎯 Concept Focus
When people say “secure the channel,” they’re talking about three distinct—but stackable—things:
How we connect (dial-up/last-mile link protocols like PPP/PPPoE; historical SLIP)
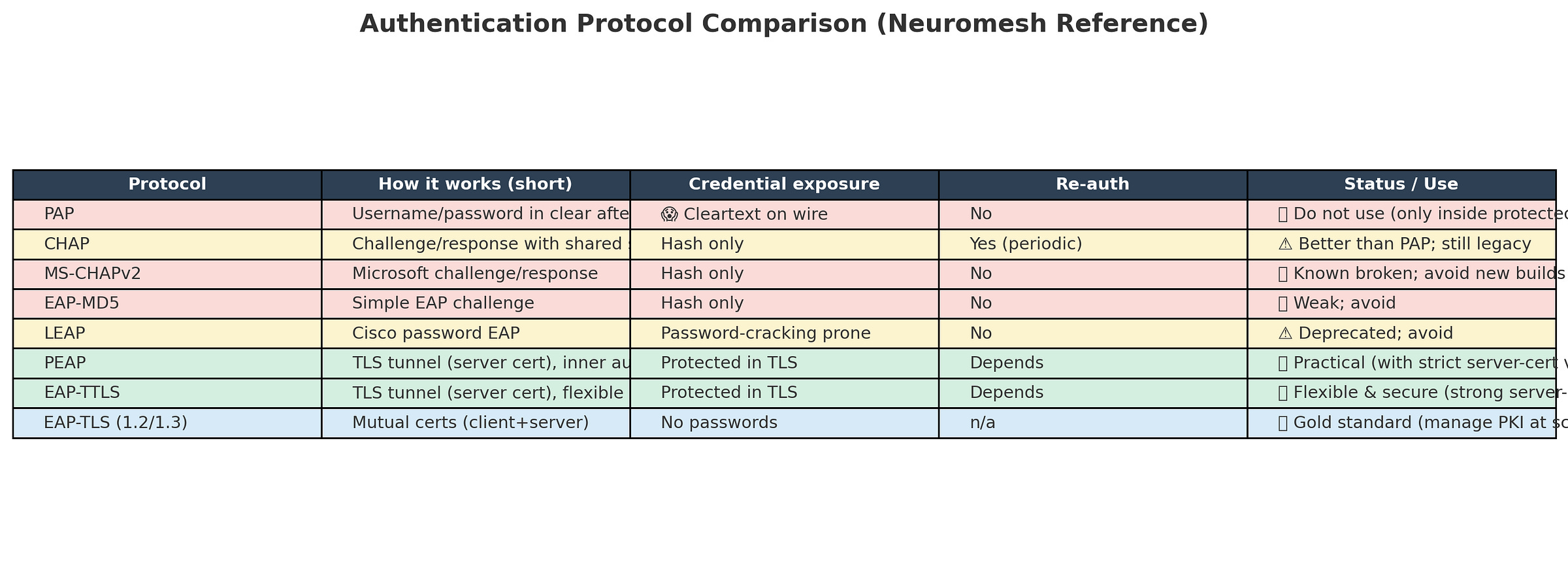
How we prove who’s who (authentication frameworks/protocols: PAP, CHAP, MS-CHAPv2, EAP & its flavors)
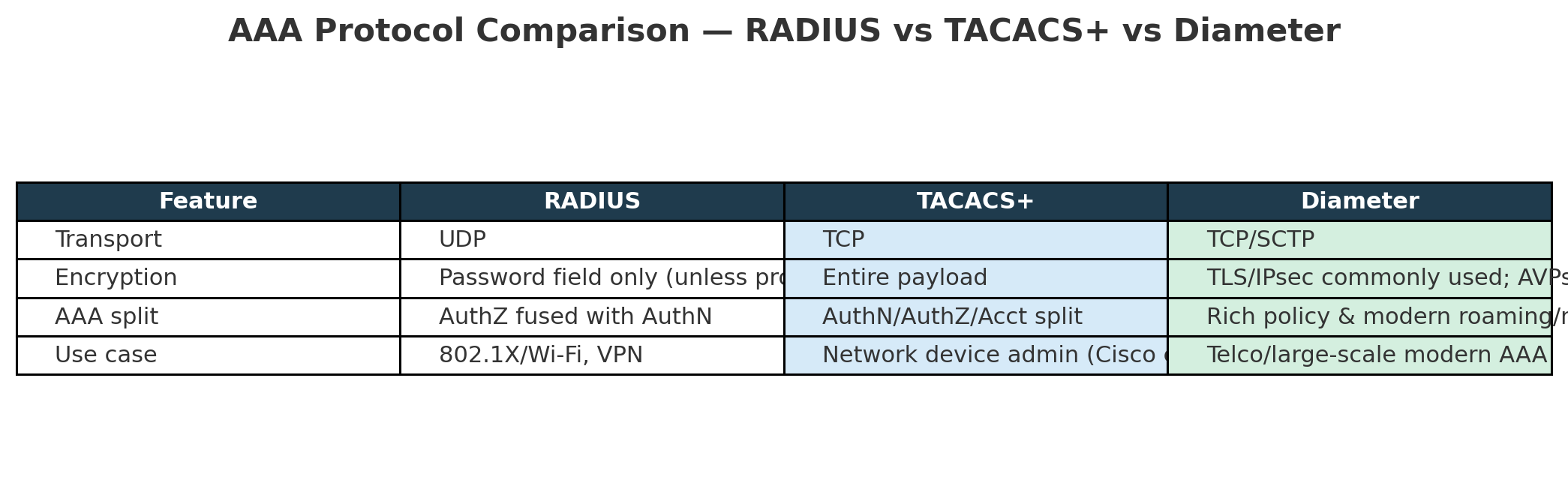
How we protect traffic in flight (communication/VPN & AAA stack: TLS, IPsec/AH/ESP, IKE/ISAKMP, plus AAA via RADIUS, TACACS+, Diameter)
Think of it like airport security:
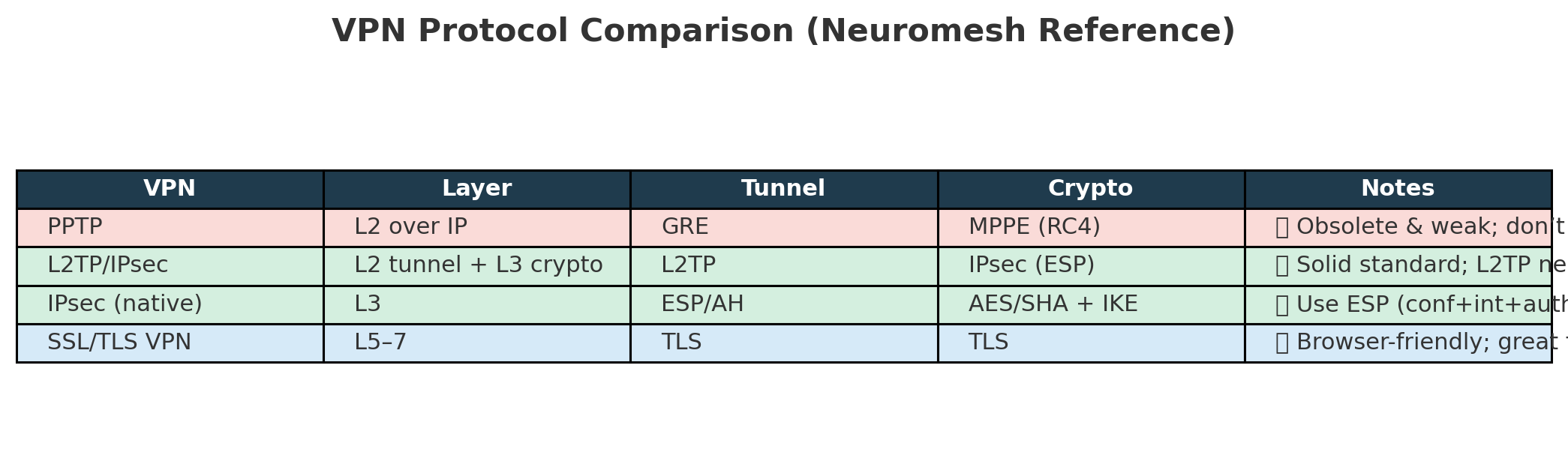
The corridor to the gate (link/tunnel: PPTP/L2TP/IPsec, SSL VPN)
Identity checks (PAP/CHAP/EAP variants)
Guards and cameras (encryption/integrity: TLS, ESP; key exchange: IKE; governance: AAA servers)
If you mix these right, you get confidentiality, integrity, availability—and traceability—without breaking usability.
Rules of thumb:
Best: EAP-TLS (if you can manage client certs).
Real-world scalable: PEAP or EAP-TTLS with strict server-certificate validation and MFA where possible.
Never: PAP/LEAP/EAP-MD5 in the clear.
Dial-up / access link protocols
SLIP: IP over serial. No auth, no error detect. History lesson only.
PPP: Framing + LCP + NCP + optional auth (PAP/CHAP). Still appears in tunnels.
PPPoE: PPP features over Ethernet (DSL last-mile). Session/billing friendly.
IPsec details that save outages:
ESP provides confidentiality + integrity + auth; AH is integrity/auth only and breaks with NAT.
Modes: Transport (host↔host) vs Tunnel (gateway↔gateway).
Keying: IKEv2 with strong suites, PFS, reasonable lifetimes, and NAT-T (UDP/4500) if traversing NAT.
AAA backends
Practical default: RADIUS for Wi-Fi/VPN auth + TACACS+ for network-device admin. Wrap either in TLS/IPsec when possible.
Brute-force, dictionary & spraying
Length over complexity (passphrases win).
Block common passwords (breached lists).
Lockouts / throttling (smart: exponential back-off, detection-friendly).
Salt + slow hash (bcrypt/scrypt/Argon2 for storage).
MFA everywhere (especially where you can’t deploy EAP-TLS yet).
🧠 Brain Ticklers
Q1. Vendor asks for quick VPN using PPTP to reach a shared file server. What’s Anya’s best response?
A. Approve PPTP if strong passwords are used
B. Approve PPTP only over GRE with ACLs
C. Reject PPTP; propose L2TP/IPsec or SSL VPN with MFA
D. Allow PPTP but force quarterly password changes
Q2. Guest Wi-Fi uses PEAP, but devices skip validating the RADIUS server certificate. What’s the actual risk?
A. None; tunnel is still encrypted
B. Evil-twin AP can harvest credentials (MITM)
C. Only DOS risk
D. Captive portal breaks
Q3. Site-to-site IPsec breaks after a new NATing firewall is installed. What’s the first fix to try?
A. Switch to AH transport mode
B. Force AES-GCM
C. Enable NAT-Traversal (UDP/4500) on both peers
D. Lower the MTU
Q4. Neuromesh wants Wi-Fi with the strongest feasible auth at scale for employee laptops. Which wins?
A. PEAP with MS-CHAPv2 and no server-cert pinning
B. EAP-TLS with managed client certificates (Intune/MDM)
C. EAP-MD5 for speed
D. LEAP for Cisco APs
Q5. Network engineers want centralized admin login on routers/switches with command-level authorization. Choose:
A. RADIUS over UDP; shared secret
B. TACACS+ over TCP; full payload encryption; per-command AuthZ
C. Diameter with IPsec
D. Local accounts with SSH keys
TakeAways
Wi-Fi (802.1X): Prefer EAP-TLS; else PEAP/EAP-TTLS with strict server-cert validation + MFA.
Remote access VPN: SSL/TLS VPN for users; L2TP/IPsec or IPsec IKEv2 for device/branch.
Site-to-site: IPsec ESP (tunnel) with IKEv2, PFS, NAT-T enabled; strong ciphersuites.
AAA: RADIUS for 802.1X/VPN; TACACS+ for network device admin; wrap in TLS/IPsec where possible.
De-list: PPTP, LEAP, EAP-MD5, bare PAP/CHAP on the wire, MS-CHAPv2 (except as inner method in a TLS tunnel while migrating).
CheatSheet
EAP Picks
Best: EAP-TLS
Practical: PEAP/EAP-TTLS (server cert validated, inner method secured, consider MFA)
IPsec Picks
ESP (not AH), Tunnel mode for gateways, Transport for host-to-host, IKEv2 + NAT-T.
AAA Picks
RADIUS (Wi-Fi/VPN)
TACACS+ (device admin)
Diameter (telco/large roaming)
Password Attacks
Length, banned lists, throttling/lockouts, salted slow hashes, MFA.
Follow The Series - IPV4 and IPV6
#CISSP #CyberSecurity #InfoSec #SecurityLeadership #WomenInCyberforce #WomenInTech #AnyaInCyberSecurity #FromDevToDefender #TechLeadership #DevSecOps #CISSPDomains #NetworkSecurity #IAM #VPN #IPsec #RADIUS #TACACS #EAP #8021X