🧱 Virtualization, Containers & Cloud
A red-team report notes that “eng build” Kubernetes nodes can break out to the host via a poorly confined privileged container. Separately, finance laptops show policy drift: host firewalls off, HIPS stale, FIM baselines missing. Meanwhile, Sales are syncing PII to a shadow SaaS.
The board just asked, “Are we safe in the cloud?”
Anya: We need one map that ties all of this together.
🎯Concept Focus
Modern enterprises don’t run on one computer or one tidy app. They run on layers: hypervisors, containers, microservices, SaaS, mobiles, and clients scattered across countries. Each layer adds power and new places to fail. Your job isn’t just to “turn on controls.” It’s to understand where isolation breaks, where defaults leak, and where shared responsibility is silently handing you the knife by the blade.
This piece distils:
Vulnerabilities of security architecture & design across virtualized stacks
Top threat actions and the mitigations that actually move risk
Virtualization vs. containers vs. microservices (security implications, not hype)
Host protection that still matters (HIPS/FW/FIM/config monitors)
Client & mobile realities (loss, misuse, weak access, eavesdropping) and concrete mitigations
Cloud fundamentals — NIST essential characteristics, service and deployment models — plus CASB as your “cloud perimeter you didn’t know you had”
Virtualization vs. Containers vs. Microservices
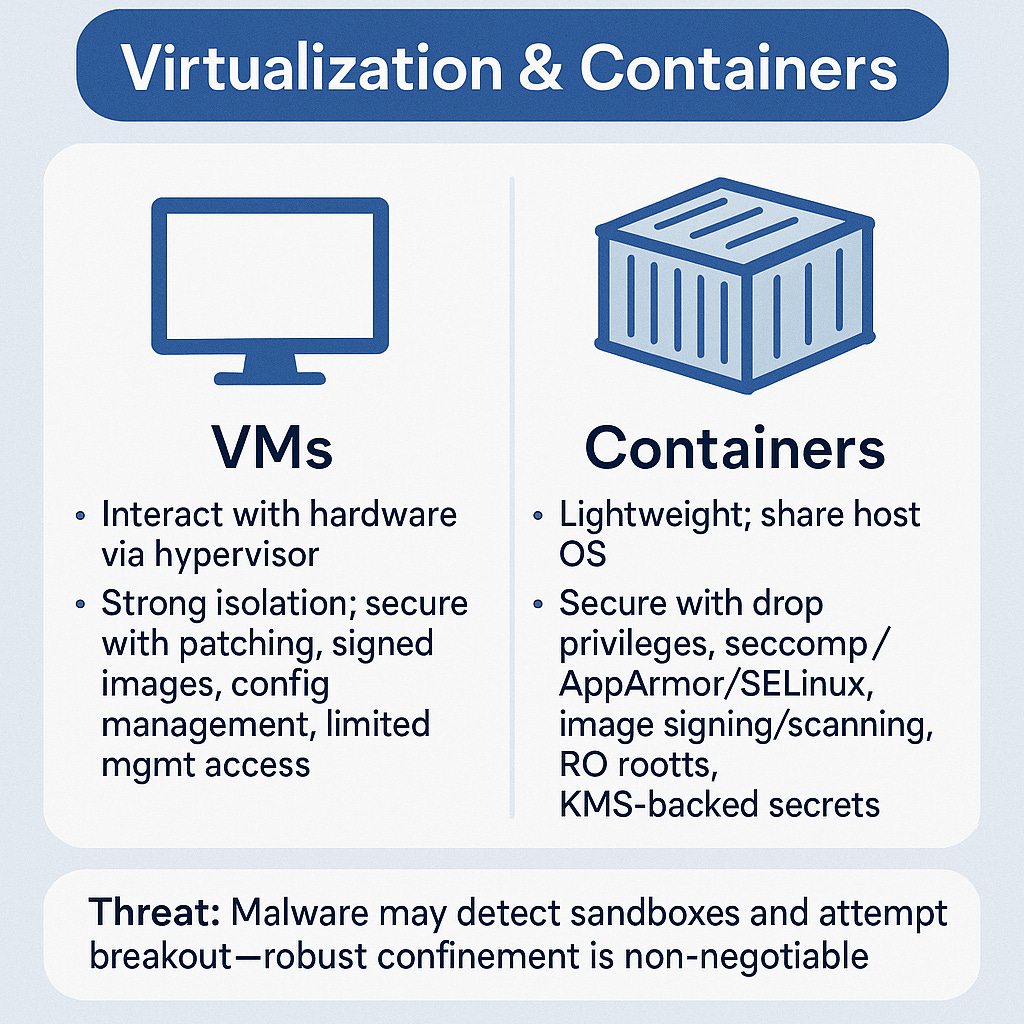
Virtual Machines (VMs)
Are Software emulation of a full OS on a hypervisor
Have Strong (guest OS boundary via hypervisor)
Risked at VM escape, snapshot sprawl, stale “gold images,” management plane exposure
Can be secured by Hardened hypervisor; signed images; config/version control; least privilege to management APIs; patch cadence
Containers
Are App + libs packaged; shares host OS kernel
Have Moderate (namespace/c/groups; weaker than hypervisor)
Risked at Privileged containers, kernel CVEs, noisy-neighbour, weak registry hygiene
Can be secured by Drop privileges; seccomp/AppArmor/SELinux; image signing & scanning; read-only root FS; secrets management
Microservices
Are Small, independent services via APIs (no shared state)
Have Logical API boundary (not a kernel/OS wall)
Risked at Over-permissive service accounts, authn/z gaps between services, SSRF, lateral movement via meshm
Can be secured by TLS service mesh, zero trust between services, least-privilege tokens, explicit schemas, rate limits
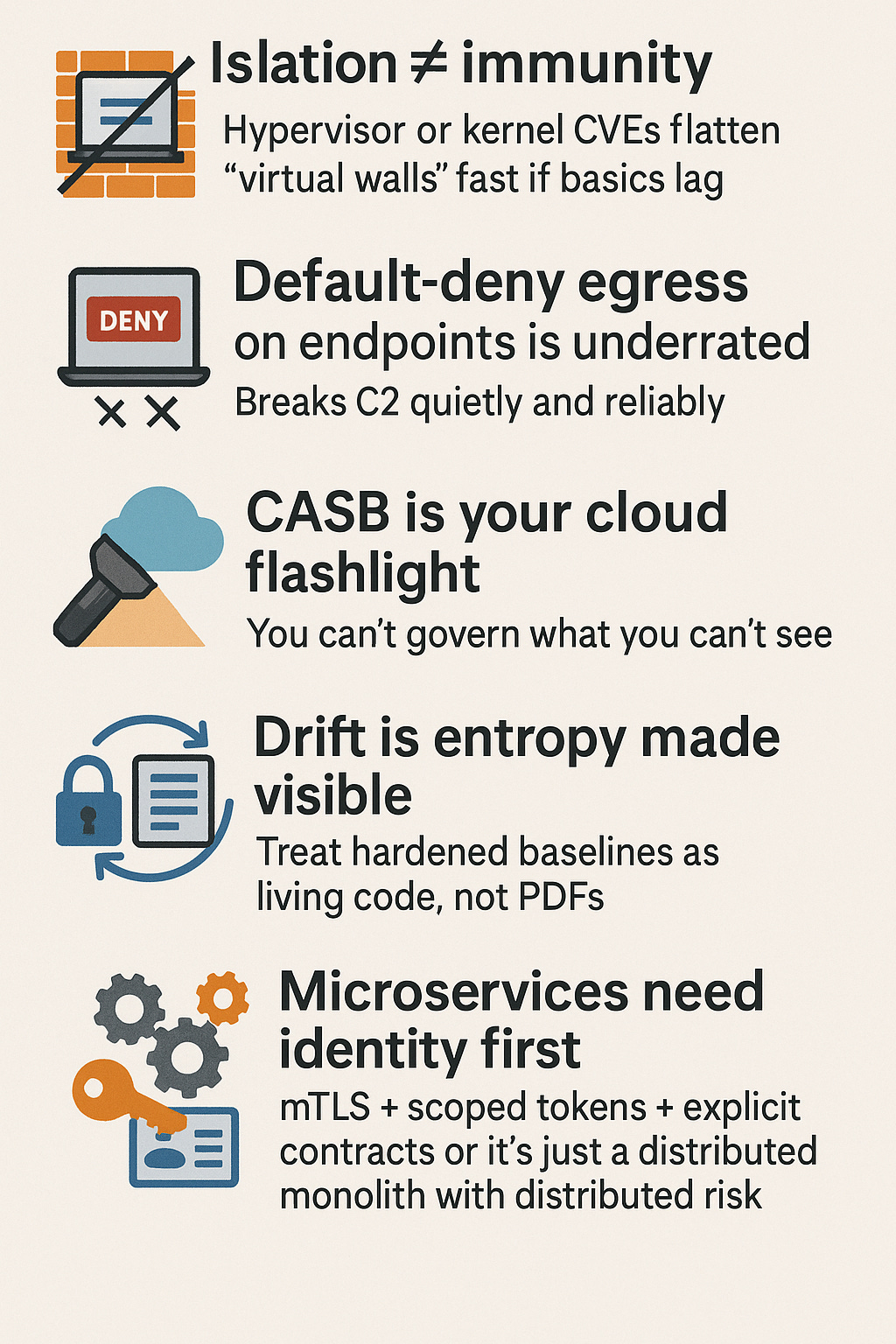
Rule of thumb: As you move “up” (containers → microservices), speed increases and implicit boundaries weaken. You must add strong identity, policy, and runtime controls.
Top Threat Actions → Mitigations
Threat Action Breakout / Escape (VM → host; container → host)
Where It Bites Hypervisor, container runtime
Why It Works Weak confinement; kernel bugs; privileged flags
Mitigations That Matter Patch hypervisor/runtime; disallow privileged containers; enable SELinux/AppArmor/seccomp; strict syscall allowlists
Threat Action Shadow IT SaaS exfil
Where It Bites Cloud apps
Why It Works Unmonitored data flows, no DLP
Mitigations That Matter CASB for discovery/DLP; per-app OAuth governance; least-privilege scopes; data classification & policy
Threat Action Config Drift
Where it Bites Endpoints, servers
Why it works “Temporary” tweaks stick
Mitigations that Matter Config & policy monitor; CIS baselines; immutable infra; drift alerts with auto-remediation
Threat Action Credential Stuffing / Phish
Where it Bites Users, service accounts
Why it works Weak MFA, token sprawl
Mitigations that Matter Phishing-resistant MFA; scoped tokens; JIT access; secrets rotation; device posture checks
Threat Action Eavesdropping / MITM
Where it Bites Mobile, Wi-Fi
Why it works Open/rogue networks
Mitigations that Matter VPN, TLS everywhere, HSTS; Wi-Fi EAP-TLS; disable legacy ciphers; MDM to kill promiscuous join
Host Protection (Endpoint Reality)
Antivirus/Anti-malware
Signature + heuristic detection
Only as good as updates + behaviour detection; don’t rely on sigs alone
HIPS
Blocks suspicious actions (buffer overflow, privilege escalation)
Complements NIPS; tune to reduce false positives
Host Firewall
Enforces inbound/outbound policy
Default-deny egress stops a shocking amount of C2
FIM
Detects unauthorized file changes with cryptographic baselines
Point at logs, configs, and app binaries; wire alerts to IR
Config/Policy Monitor
Detects drift from hardened baselines
Make baselines living artifacts; auto-revert when feasible
Client & Mobile: Risks and Mitigations
Client Risks: physical loss, misuse, unapproved software, phishing clicks, local secrets.
Mobile Risks: loss/theft, weak access controls, unencrypted data, eavesdropping (MITM/fake APs), limited onboard security.
Controls that actually move risk (Neuromesh profile):
Patch/Update: OS, apps, firmware — automate.
Network Controls: segmentation; NIDS/NIPS; egress allowlists for SaaS.
Endpoint Security: AV/EDR + HIPS + host FW + full-disk encryption.
Monitoring: central logs + alerts (failed logins, suspicious child processes).
User Education: short, high-signal modules (phish drills, USB hygiene).
MDM for Mobile: only manageable devices get access; push policies; encrypt profiles; idle timeout; screen locks; remote wipe; camera/Bluetooth lockdown where sensitive; block jailbroken/rooted; geofencing for high-sensitivity roles.
Cloud Security — NIST, Models, and Reality
Essential Characteristics (NIST):
On-demand self-service
Broad network access
Resource pooling (multi-tenancy)
Rapid elasticity
Measured service.
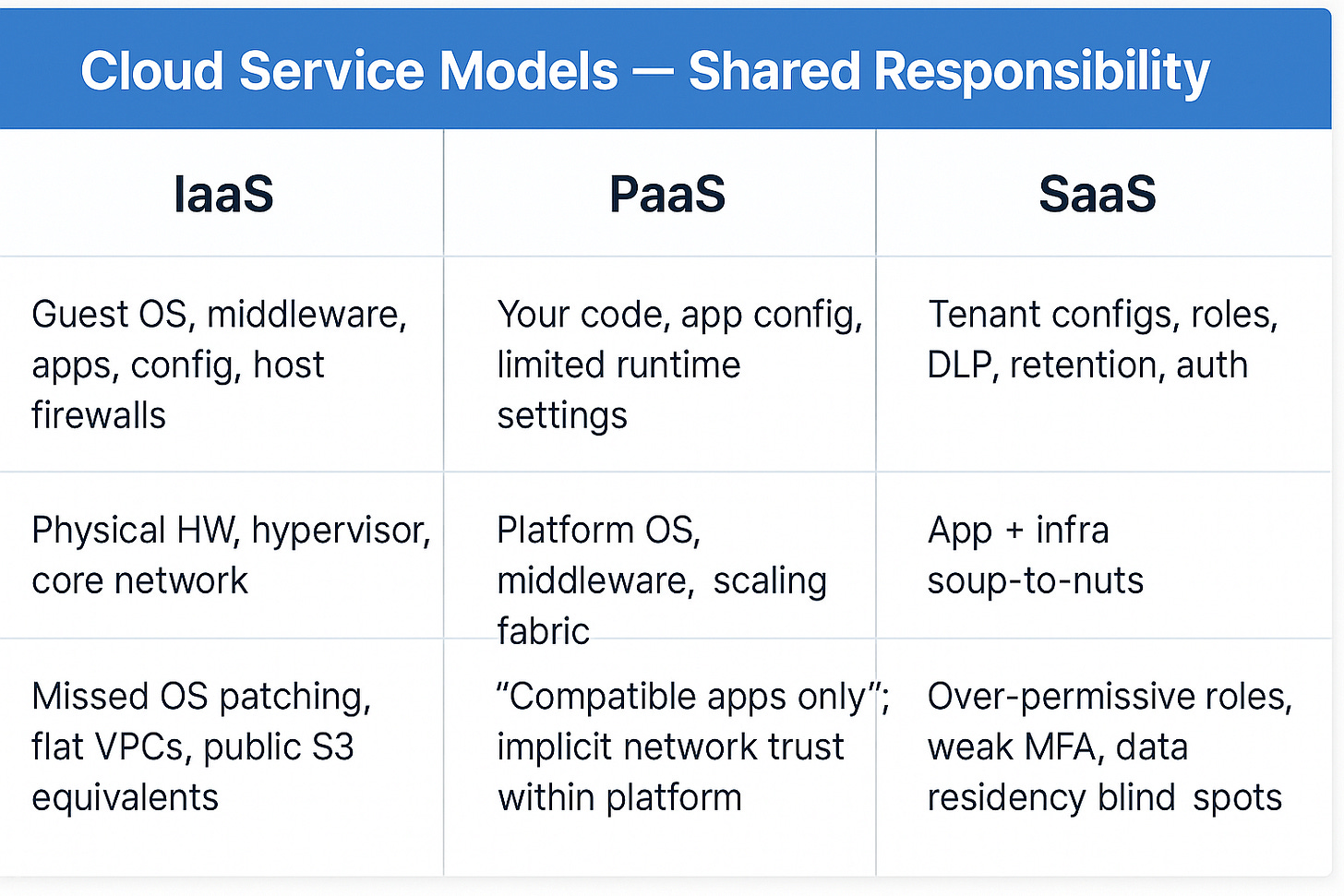
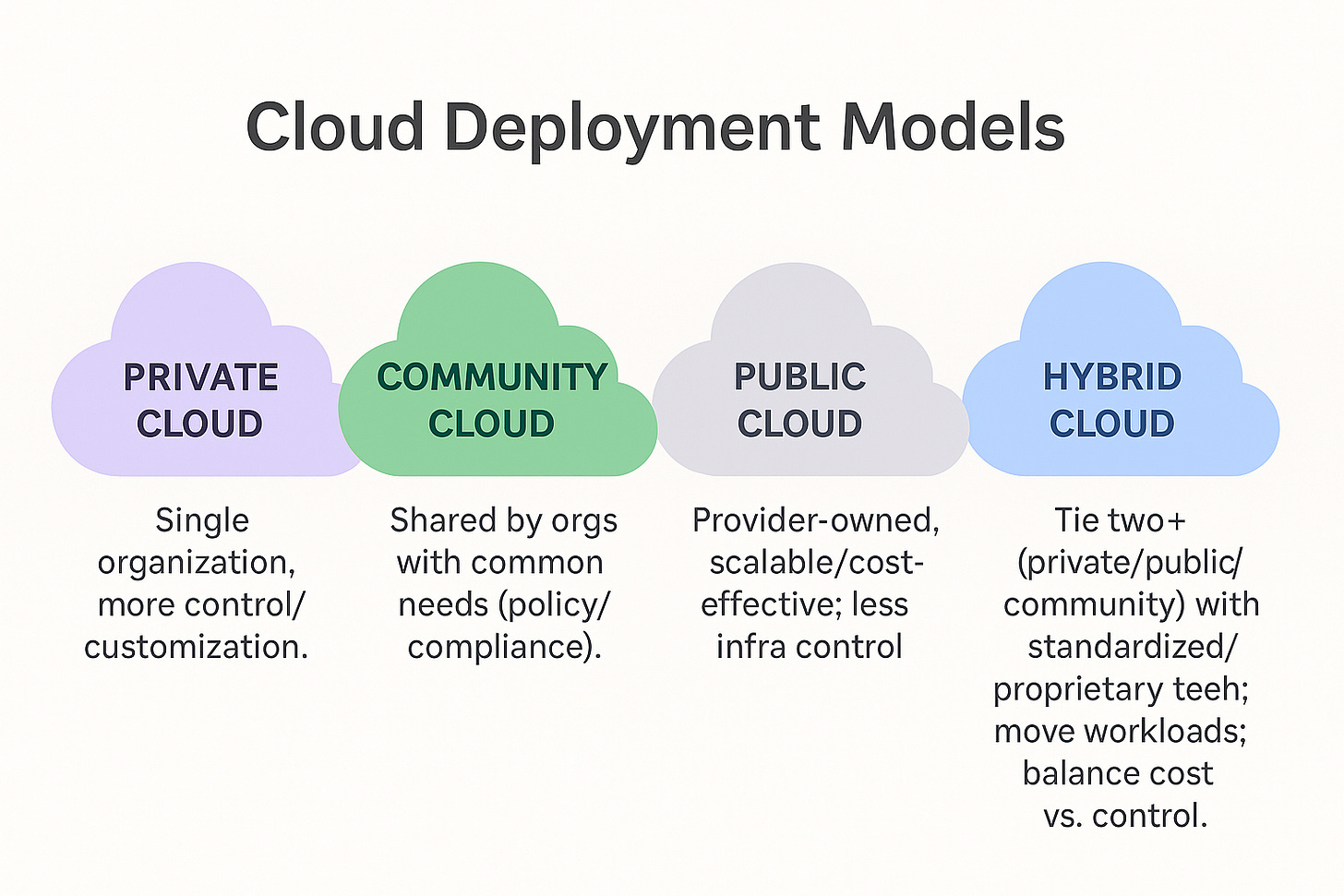
Service Models & Responsibility Split
CASB (Cloud Access Security Broker):
Your visibility and policy engine between users/devices and cloud services.
Discover shadow apps, usage patterns.
Protect with DLP, encryption, token governance.
Enforce access policies; monitor OAuth scopes; inline or API-mode.
Detect threats across IaaS/PaaS/SaaS (Salesforce/Google Workspace/Azure/AWS).
A Typical Usage of all concepts at Neuromesh
Virtualization & Containers
Anas maintains bare-metal hypervisors for production DB VMs. We harden the hypervisor, sign and version “known-good” VM images, and remove dormant snapshots.
In hosted virtualization (legacy lab), we reduce exposure by moving admin tools behind a bastion and enforcing MFA + per-command logging.
On Kubernetes, we:
Ban privileged containers and use seccomp profiles;
Enforce read-only root filesystems;
Apply AppArmor/SELinux;
Require image signing + scanning before deploy;
Rotate secrets with a managed KMS and use CSI secrets store.
Microservices
Leila designs service-to-service mTLS with SPIFFE/SPIRE identities.
We replace wildcard tokens with scoped, short-lived JWTs; add rate limiting and schema validation on every ingress/egress boundary.
“No shared state” is enforced by design reviews; any accidental state coupling is flagged in pipelines.
Endpoints (Finance Laptops)
Marcus enables host firewalls (default-deny egress), ships EDR + HIPS, and restores FIM baselines for config/log protection.
Config monitor watches for “temporary exception” gravity wells. Drift creates a ticket and auto-reverts for high-risk keys.
Susan’s BYOD policy resets: only centrally managed devices get access; MDM enforces encryption, lockouts, and remote wipe.
Cloud & CASB
Shadow SaaS discovered via CASB is either sanctioned (with DLP & retention) or blocked.
In IaaS: no flat networks; subnet segmentation, security groups as deny-by-default, VPC egress via proxied gateways with URL categories.
In SaaS: phishing-resistant MFA, least-privileged roles, tenant audit logging to SIEM, and data classification aligned to DLP rules.
Hybrid: burst read-only workloads to public cloud; sensitive writes stay private. Movement via standardized APIs, audited and measured.
🧠 Brain Ticklers
Q1. Red team shows a container can start with
--privilegedon Neuromesh’s CI runners. What is the most effective first mitigation?
A. Add more AV signatures to runner hosts
B. Remove privileged container capability; enforce seccomp/AppArmor; read-only rootfs
C. Move CI runners to a bigger VM
D. Enable HSTS on the corporate website
Q2. Finance laptops show host firewalls disabled and FIM baselines missing after a “temporary” troubleshooting change. Which control best prevents re-occurrence?
A. Annual security awareness training
B. Config/policy monitor with auto-revert to hardened baselines
C. New laptop model with faster CPUs
D. Weekly manual checklist by helpdesk
Q3. Sales is using an unsanctioned cloud storage app to share prospect data. What provides visibility and enforcement with least friction?
A. Block all internet access except corporate site
B. CASB discovery + DLP policies + OAuth scope governance
C. Move Sales to private cloud VMs
D. Ask users to email files instead
Q4. Neuromesh runs a payment microservice architecture. An incident shows lateral movement via over-permissive service tokens. Best architectural fix?
A. Increase pod CPU limits
B. Centralize all services into a monolith
C. Mutual TLS identities (SPIFFE), least-privilege tokens, and per-service ABAC
D. Replace Kubernetes with bare-metal servers
Q5. Travelers from the Luxembourg sales team work from airports and cafés. What policy set most reduces mobile eavesdropping risk without breaking workflows?
A. Disable Wi-Fi globally on mobiles
B. Require VPN; enforce TLS; MDM-pushed Wi-Fi profiles; block open SSIDs; screen lock + remote wipe
C. Ask employees to be careful with Wi-Fi
D. Move all apps to on-prem only
Cheat Sheet
Follow the series - Secure Architecture
#CISSP #CyberSecurity #InfoSec #SecurityArchitecture #CloudSecurity #Virtualization #Containers #KubernetesSecurity #Microservices #EndpointSecurity #MobileSecurity #CASB #ZeroTrust #WomenInCyberforce #WomenInTech #AnyaInCyberSecurity #FromDevToDefender #TechLeadership #DevSecOps #CISSPDomains